Scott jones head of the canadian centre for cyber security and cse deputy chief of it security looks on during an announcement on the national cyber security strategy in ottawa june 12 2018.
National cyber security centre encryption at rest.
1 national cyber security centre previously cesg.
2 2 data centre security.
While most modern devices have encryption built.
Locations used to provide cloud services need physical protection against unauthorised access tampering theft or reconfiguration of systems.
The processing of personal data is naturally associated with a certain degree of risk.
Cyber aware coronavirus phishing 5g.
Find a list of the broad range of cyber security related topics that our advice and guidance covers.
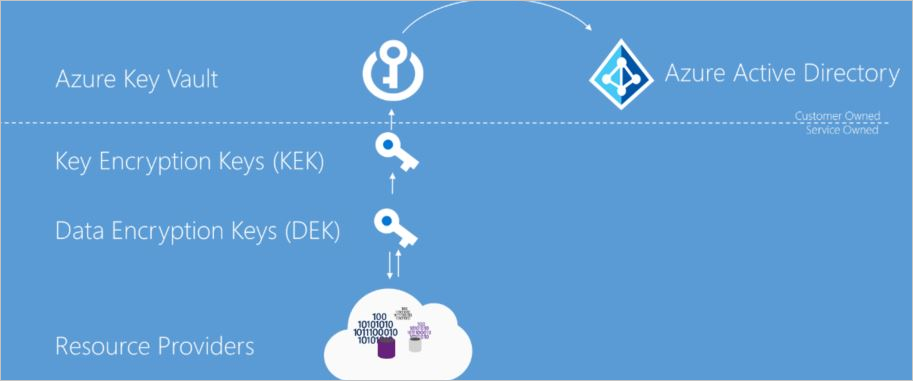
Data in transit is protected between your end user device s and the service.
Companies can reduce the probability of a data breach and thus reduce the risk of fines in the future if they chose to use encryption of personal data.
You should be sufficiently confident that.
This isn 2018 02 supersedes isn 2017 08 which was issued in december 2017.
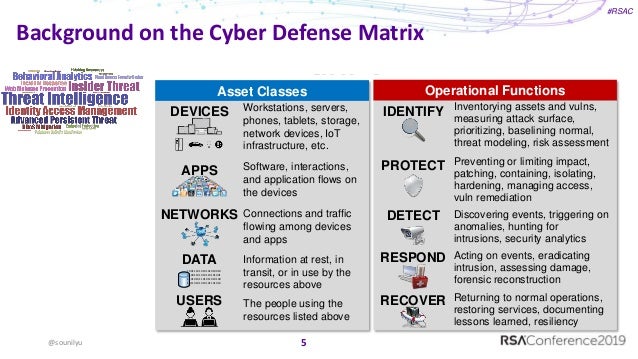
Make sure devices encrypt data at rest to protect data on the device if it is lost or stolen.
This guidance recommends steps to take if your organisation is introducing or scaling up the amount of home working.
Inadequate protections may result in the disclosure alteration or loss of data.
By contrast data in motion is the data moving through a network such as via email.
This industry security notice isn provides interim advice on approved acceptable endorsed encryption products for rsmd and describes planned activity for further work in this area.
Cyber security alert issued following rising attacks on uk academia.
This should be achieved through a combination of.
For official information about coronavirus please refer to trusted resources such as the public health england or nhs websites.
Network protection denying your attacker the ability to intercept data.
Now the uk s national cyber security centre.
Data at rest refers to the data that does not move such as that stored on a laptop.
Encryption at rest overlaps with encryption in motion but focuses on protecting the data that is at rest.
The national cyber security centre helping to make the uk the safest place to live and work online.
Encryption denying your attacker the ability to read data.